Create your own VPC in AWS
AWS provides you with a default VPC in each region. There are cases however where you will need a new VPC. Of course you can use the VPC wizard, but it can also be really rewarding to be able to set up your VPC manually. Let’s set up one.
Creating your VPC
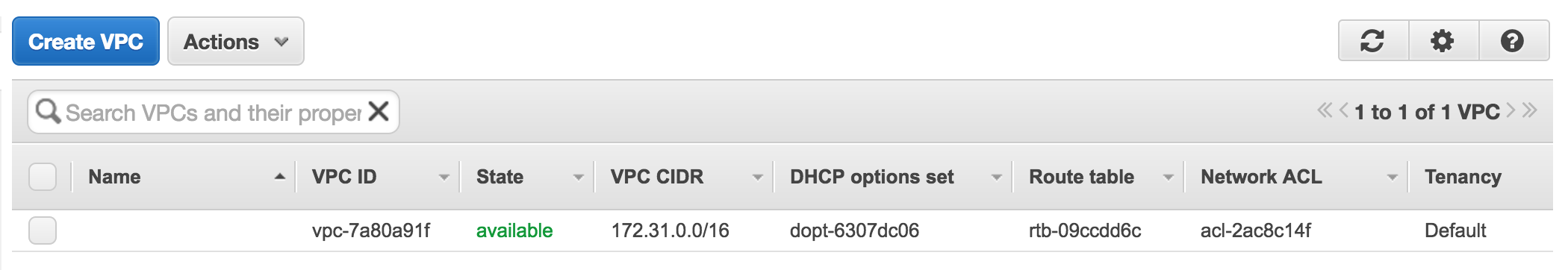
After logging in to your AWS Console, head over to the VPC section. Within the VPC overview, you will see an existing VPC. This is your default VPC created by Amazon. You can click “Create VPC” to create a new one.
First you can define a name for your VPC. Next you have to define the CIDR block. This is the IP range which your VPC will use. The most common CIDR block is 10.0.0.0/16. Finally you have to define the tenancy of the VPC. By setting it to default, your VPC will be on shared hardware. You can also put your VPC on dedicated hardware, but this will cost you extra.
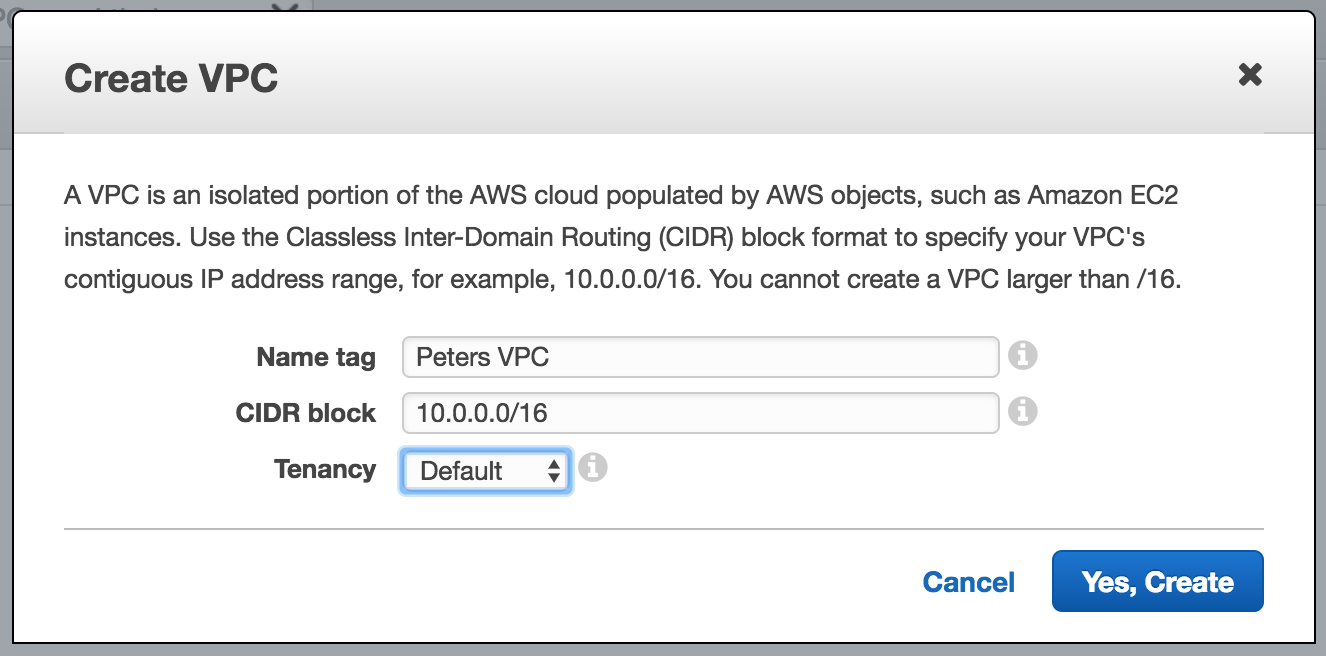
After clicking the create button, 4 things will be created;
- The VPC itself
- A Route table
- A Network ACL
- A Security group
You can find all of these items in the corresponding menu items. We can now continue creating some subnets and an internet gateway.
Note: You can find the recommended CIDR blocks from Amazon over here.
Subnets
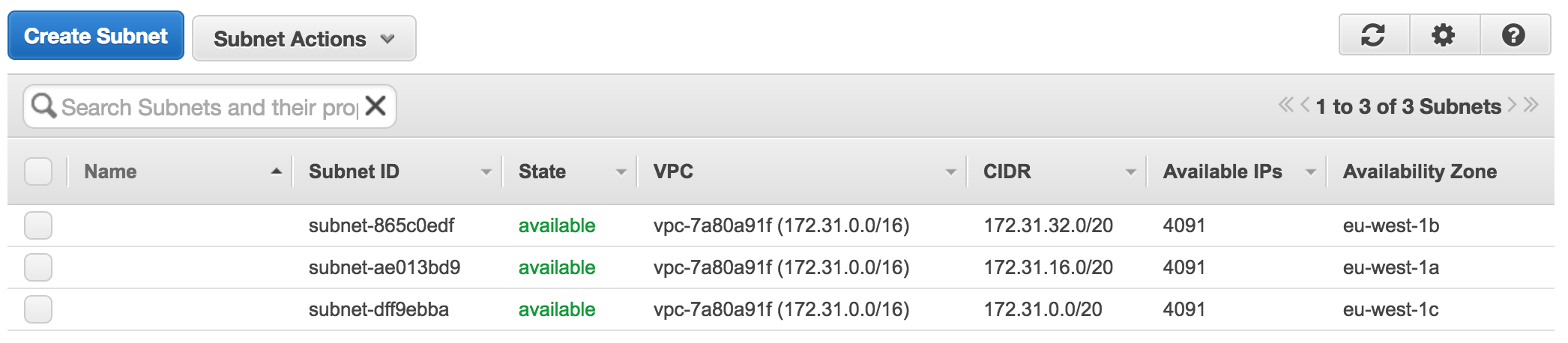
We can continue with our VPC by creating multiple subnets. Open up the subnets overview from the menu. The subnets you will find in the overview are part of the other already existing VPC. Click “Create Subnet” to create a new one.
First we define a name for our subnet. I mostly name the subnets for their CIDR block and availability zone. Next you have to make sure to choose the VPC you just created and choose an availability zone. I mostly create one subnet per each availability zone. In this case I am creating a VPC in Ireland, which has 3 availability zones. Therefor I create a subnet with the following CIDR blocks;
- 10.0.1.0/24 in eu-west-1a
- 10.0.2.0/24 in eu-west-1b
- 10.0.3.0/24 in eu-west-1c
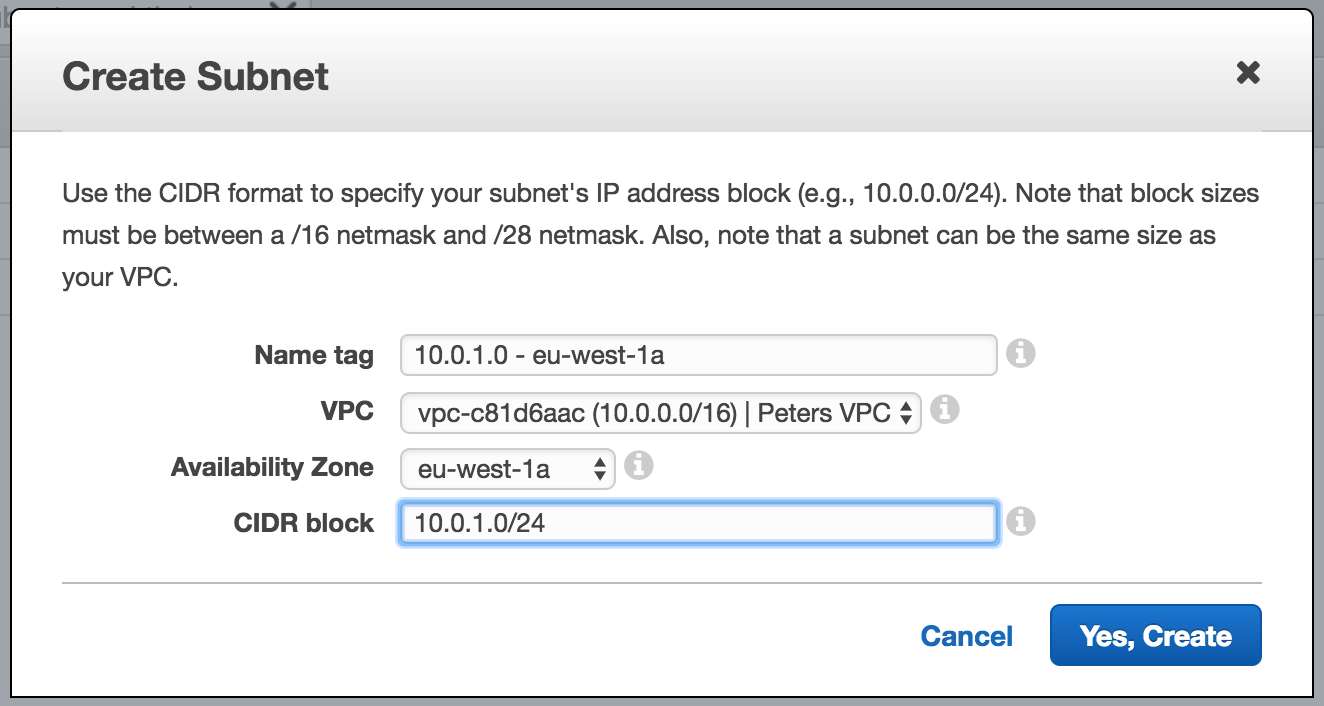
Note: AWS reserves some IP addresses within a subnet. You can find a full list, including a subnet calculator over here.
Internet Gateway
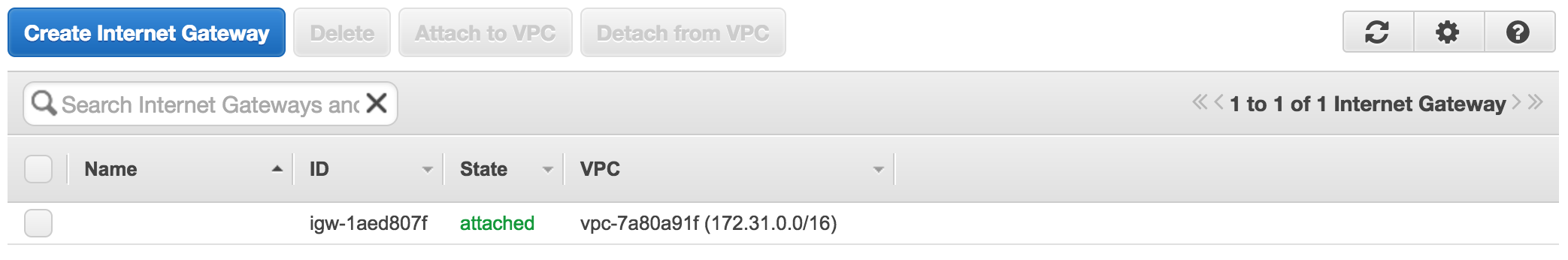
All the subnets which we created up till now are all private. To make one or more subnets public, we have to attach them to the internet. Therefor we head to the internet gateway page and create a new one.
Creating a new internet gateway is easy. We just have to define a name for it.
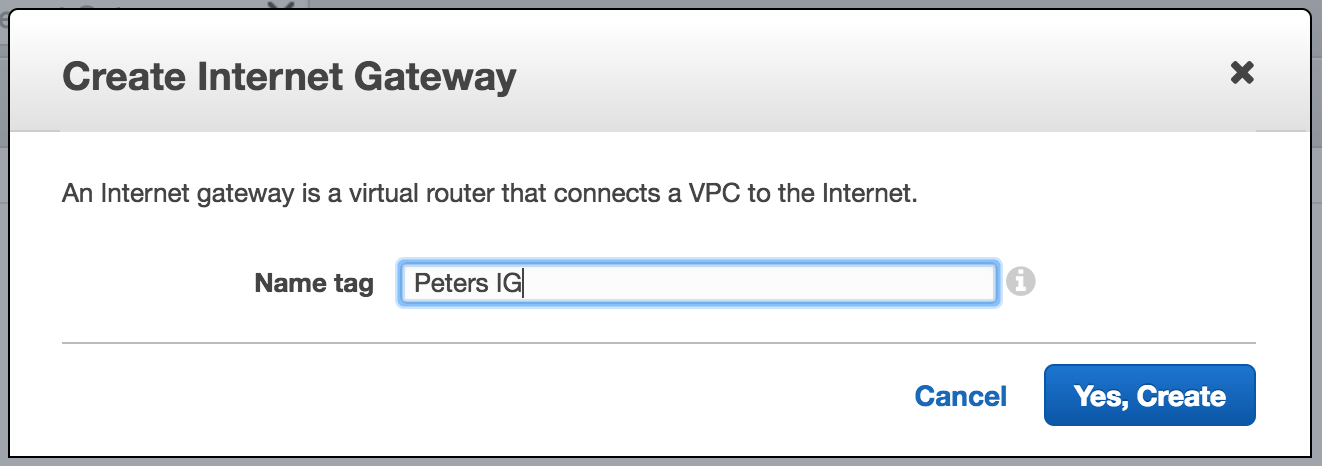
Finally we have to attach the internet gateway to our VPC by selecting our newly create internet gateway and clicking “attach to VPC”.
Route tables
The next thing we have to do is to define a way out to the internet in our route tables. As noted before, a default route table was created at the moment we defined our VPC. However, we leave this route table as it is since it’s now marked as private. We create a new route table by clicking “create route table”.
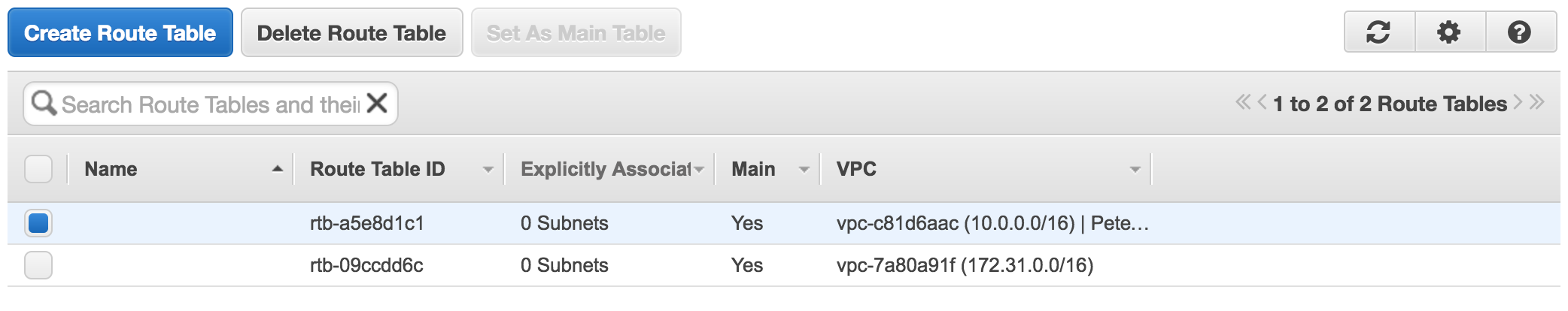
We only have to define a name for our route table and choose our correct VPC.
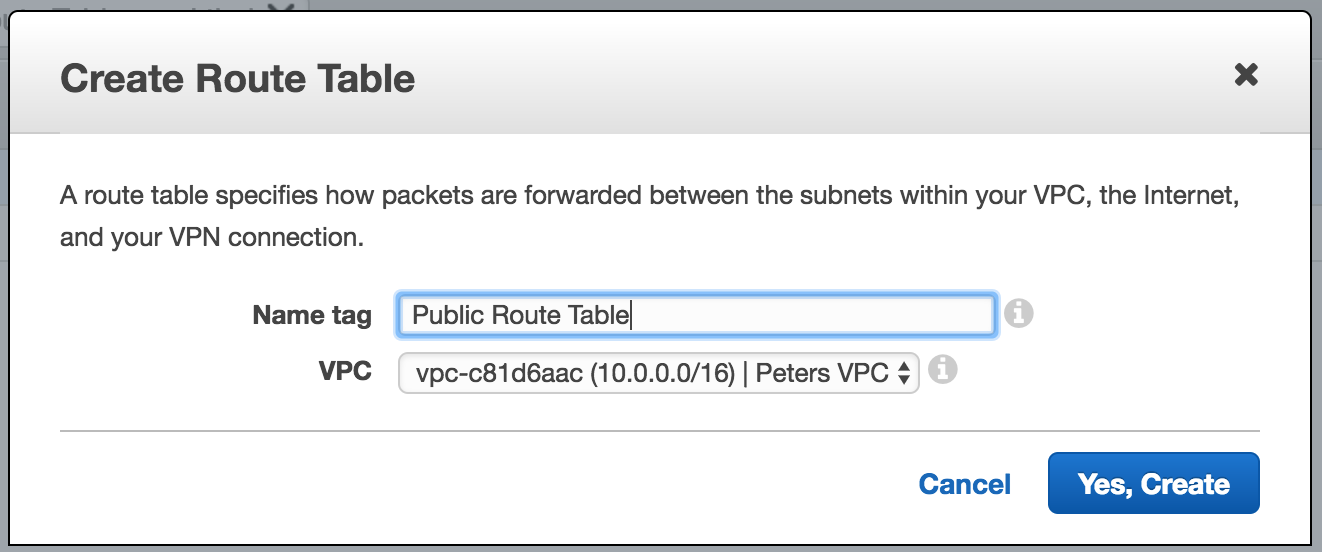
Now we have to define a route in this route table, to the internet. We do this by adding a new route with destination 0.0.0.0/0 and select our internet gateway as the target.
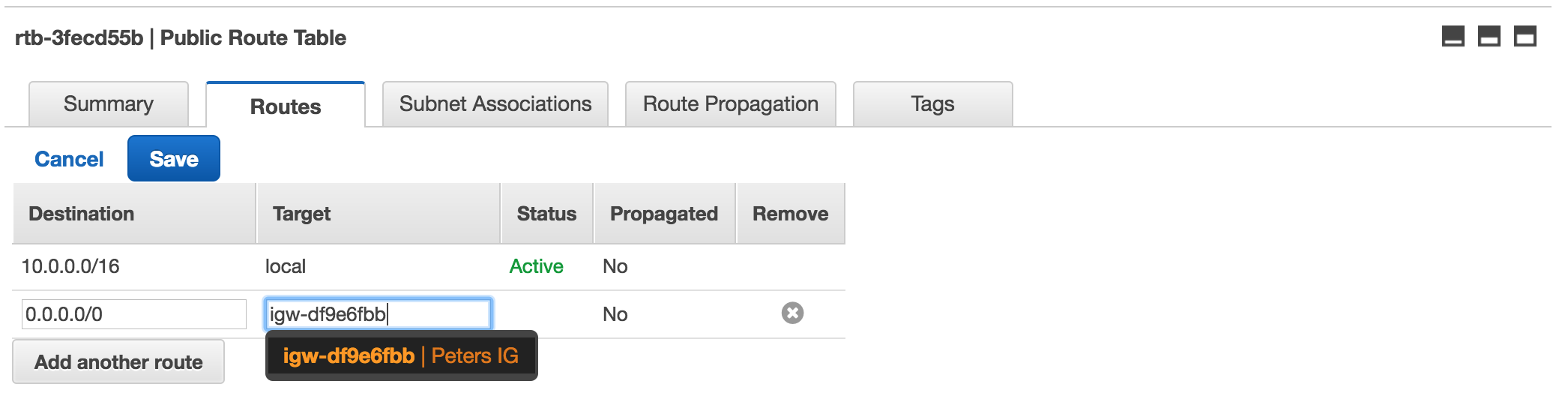
Up till now, all subnets are still associated with the main route table, which is the default route table created earlier. We therefor head to “subnet associations” tab and click “edit”. You can now define which subnets can go public.
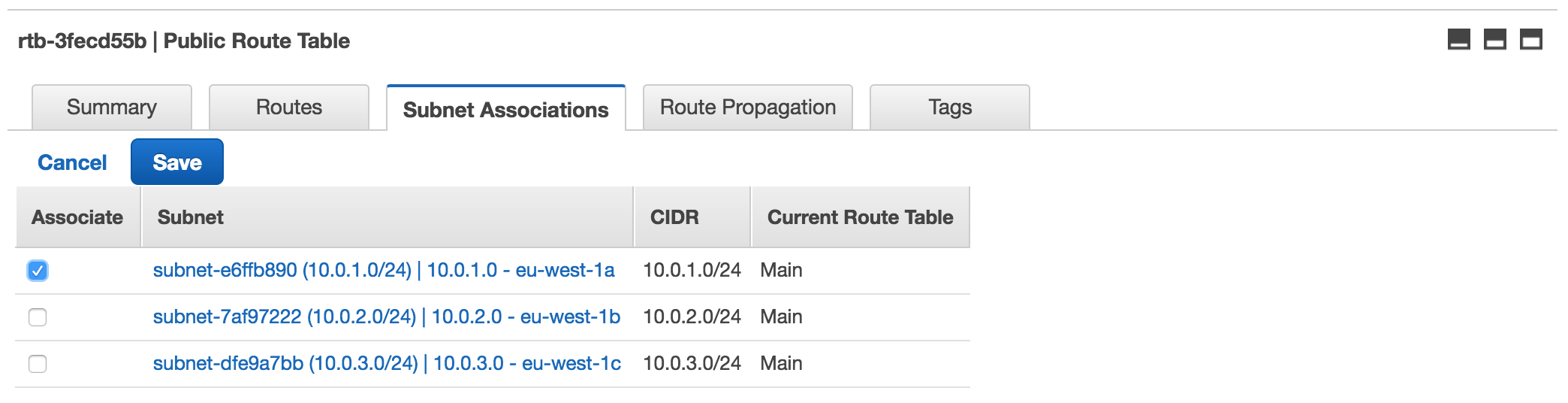
I would recommend only allowing one subnet to the internet. With a NAT instance you can make sure that still all EC2 instances can connect to the internet, while not exposing them. More on that in a later article.
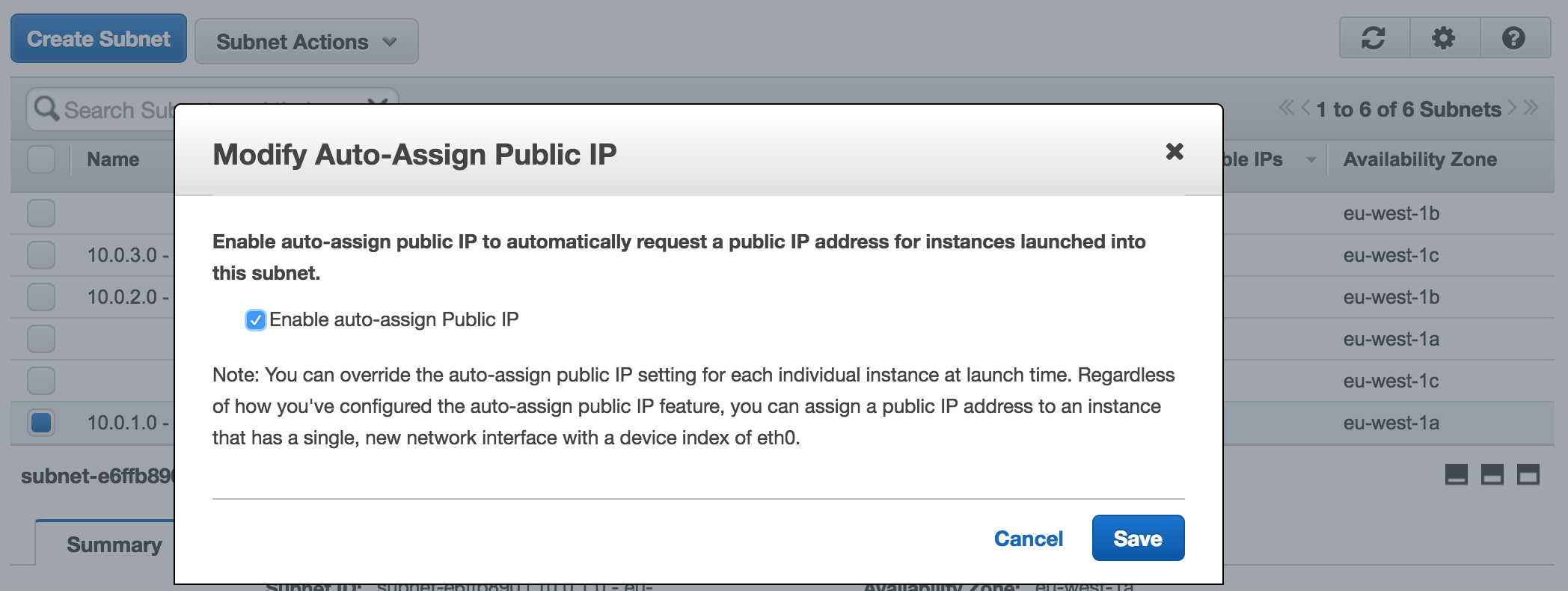
The last step we have to do, is to make sure that all EC2 instances created within our public subnet, automatically get an IP assigned. We therefor head to the subnet overview, select our public subnet and click “Modify auto-assign Public IP” within “Subnet Actions”. Check the box to enable the auto assigning of IPs.
That’s it! We created our very own VPC with multiple subnets in which we can deploy new EC2 instances. In an upcoming article we will be deploying a NAT instance and talk about connecting two VPCs in different regions with Strongswan.